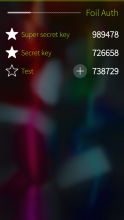
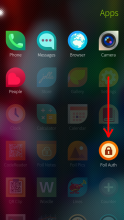
Foil Auth
Secure OTP (One-Time Password) generator for Sailfish OS.
Foil Auth keeps secret authentication keys encrypted with your Foil password. Supports time-based (TOTP), counter-based (HOTP) and Steam passwords. Tokens can be shared and imported via QR codes.
Foil password (and the RSA encryption key ~/.local/share/foil/foil.key) is shared with Foil Pics and Foil Notes. Encrypted authentication keys for OTP generation are stored in ~/Documents/FoilAuth.
The format of the encrypted file is described here.
Note that you can add your encrypted files and the Foil key to the backup with the help of My Backup app.
Source code: https://github.com/monich/harbour-foilauth
Category:
Keywords:
Application versions:
Changelog:
- 1.1.15 (Apr 21 2023)
- Updated Swedish translation (Åke Engelbrektson) - 1.1.14 (Apr 19 2026)
- Italian translation (legacychimera247)
- Minor bug fixes - 1.1.13 (Apr 6 2026)
- Norwegian bokmål translation (Frank Paul Silye) - 1.1.12 (Sep 23 2025)
- Made organize page headers scrollable
- Fixed wakeup criteria for auto-lock
- Improved Base32 handling
- Freshened up Foil UI - 1.1.10 (Oct 10 2024)
- Do not run the countdown timer at startup
- Added UI for configuring auto-lock delay
- Use wakeup timer for auto-lock
- Allow to scan QR code with the front camera - 1.1.9 (Jul 22 2023)
- Fixed countdown timer on the cover page - 1.1.8 (Jul 22 2023)
- Actually use timeshift
- Fixed couple of Steam token issues - 1.1.7 (May 7 2023)
- Added support for Steam variant of TOTP - 1.1.6 (Apr 14 2023)
- Improved QR code scanning
- Slightly redesigned QR code page
- Request focus for password field at startup
- Updated Swedish translation (Åke Engelbrektson) - 1.1.5 (Jan 15 2023)
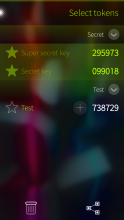
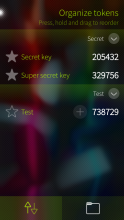
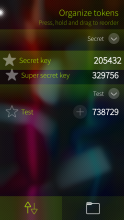
- Support for token groups
- New UI for reordering tokens
- Updated Polish translation (Atlochowski) - 1.1.4 (Sep 26 2022)
- Fixed a problem with import via QR code - 1.1.3 (Aug 17 2022)
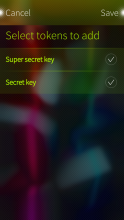
- Implemented import of multiple tokens
- Freshened up the UI
- Removed MD5 support - 1.1.2 (Jul 25 2022)
- Tweaked token creation workflow
- Switched QR-code decoding from zxing to zbar
- Properly support non-ASCII labels - 1.1.1 (Jun 13 2022)
- Allow to turn autolock off - 1.1.0 (Mar 20 2022)
- Opt out of sandboxing (no more Jolla Store updates!)
- Improved QR code scanning performance
- Minor UI tweaks
- Added Chum metadata - 1.0.21 (Nov 15 2021)
- Load libcrypto.so dynamically - 1.0.20 (Nov 5 2021)
- Link OpenSSL 1.0 statically for compatibility with Sailfish OS 4.3
- Updated Polish translation (Atlochowski)
- Tweaked selection page - 1.0.19 (Oct 10 2021)
- Support for HOTP (counter-based) passwords
- Copy password to clipboard on tap - 1.0.18 (Jul 30 2021)
- Allow to choose HMAC digest algorithm
- Generate QR codes with lower error correction level
- Reworked QR code scan UI transitions
- Don't ignore issuer of scanned tokens
- Export or delete multiple tokens at once - 1.0.17 (Apr 18 2021)
- Support for reading otpauth-migration QR-codes - 1.0.16 (Feb 23 2021)
- Hungarian translation (@1Zgp) - 1.0.15 (Jan 9 2021)
- Tweaked remorse items a bit
- Integration with My Backup - 1.0.14 (Dec 20 2020)
- Fixed flashlight - 1.0.13 (Dec 11 2020)
- Fixed QR code scanning on Sailfish OS 4.0
- Updated libqrencode to v4.1.1 - 1.0.12 (Nov 30 2020)
- Added "Show QR code" context menu item
- Display QR code full screen when it's tapped - 1.0.11 (Nov 16 2020)
- Updated Polish translation (Atlochowski) - 1.0.10 (Nov 15 2020)
- Adapted to recent changes in Sailfish OS
- Polished landscape layouts - 1.0.9 (Oct 12 2020)
- Fixed a problem with initial update of current passwords
- More dialog titles - 1.0.8 (Oct 7 2020)
- Added German translation (Samuel Kron)
- Use stronger SHA256 digest for signature
- Tweaked password change UI - 1.0.7 (Jan 3 2020)
- Support for scanning inverted QR codes
- Autolock is delayed by 15 seconds
- Miscellaneous UI tweaks - 1.0.6 (Nov 12 2019)
- Freshened up the UI - 1.0.5 (Apr 22 2019)
- Query the actual maximum zoom from the camera
- Improved French (Quentí) and Polish (Atlochowski) translations - 1.0.4 (Apr 12 2019)
- French translation (Quentí) - 1.0.3 (Apr 11 2019)
- Swedish translation (Åke Engelbrektson) - 1.0.2 (Apr 11 2019)
- Chinese translation (@dashinfantry) - 1.0.1 (Apr 10 2019)
- Polish translation (Atlochowski) - 1.0.0 (Apr 10 2019)
- Initial version











Comments
PawelSpoon
Sat, 2025/09/27 - 11:24
Permalink
Great app ! Saved my ass at work (to avoid android)
myjollaph
Fri, 2023/08/11 - 10:34
Permalink
Hi, I love this App and use it on daily bases -> thanks so much
One thing though, and sorry if you've already answered/explained this earlier, but I was wondering if it could be possible to store the content of ~/Documents/FoilAuth on the SD card instead of the phone or do you think that if I create a sym link it would still work, even after reboot? Cheers
slava
Fri, 2023/08/11 - 17:04
Permalink
Symlink should work as long as the target directory/volume is there.
poetaster
Wed, 2023/06/14 - 23:09
Permalink
Just a big thank you. As is true for all your apps, it's as nice under the hood as it is to use!
slava
Thu, 2023/06/15 - 20:30
Permalink
You're welcome)
mp0
Mon, 2023/05/29 - 23:49
Permalink
The worst application I used. Lost a lot of accounts because of using it. It asks for password, which I forget after 1 minute. Next day, I need to create a new password, because the previous one is forgotten. And this lasts for months.
ade
Wed, 2023/05/31 - 20:43
Permalink
SailOTP (https://openrepos.net/content/seiichiro0185/sailotp) is an alternative without a password.
slava
Thu, 2023/06/01 - 04:13
Permalink
Yeah, the whole point of this one is to protect OTP secrets with a password. Which some may argue isn't that important if you have the entire user partition encrypted (mine isn't).
slava
Wed, 2023/05/31 - 01:15
Permalink
This app is not intended to be used by people who can't remember their passwords))
poetaster
Fri, 2023/02/03 - 12:28
Permalink
Just wanted to note that fail auth works really well. Thanks!
jolla4ever
Tue, 2022/08/23 - 00:55
Permalink
@slava, a must have programm. Thank you very much!
slava
Fri, 2022/06/17 - 01:48
Permalink
If Foil Auth settings page doesn't show up, you may have to fix
/usr/share/jolla-settings/pages/ApplicationsGrid.qml(look forroot.openSandboxed) or you can modify/apps/harbour-foilauth/autoLockfrom the command line e.g.dconf write /apps/harbour-foilauth/autoLock false. Sadboxing may have messed things up in the application settings area too.norayr
Thu, 2021/11/04 - 19:06
Permalink
3vixan, i did that once and it worked.
lqramen
Thu, 2021/11/04 - 13:32
Permalink
SF 4.3, cannot install due to missing libcrypto.so.1
lpr
Sun, 2021/11/07 - 21:53
Permalink
https://openrepos.net/sites/default/files/packages/7598/openssl-libs10-1... will give you libcrypto.so.1
slava
Thu, 2021/11/04 - 14:47
Permalink
I swear I didn't delete it)) Seriously speaking, it looks like I have no choice but to link openssl statically in order to keep the app compatible with both systems not having libcrypto.so.10 and those not having libcrypto.so.1.1 which sadly will make the app HUGE. That sucks. It really does. Especially considering that libcrypto.so.10 was allowed in Jolla Store.
In the meantime, you can find a build linked against your favorite release from Chum. With the introduction of SFOS 4.3, releases are no longer backward compatible. It's hard to describe how I detest that.
lpr
Sun, 2021/11/07 - 21:55
Permalink
another round here: no, don't do that but link dynamically to openssl1.1 and jolla1 users just install openssl from here: https://openrepos.net/content/lpr/curl
slava
Sun, 2021/11/07 - 22:09
Permalink
And another round here: Chum is your friend if you want an armv7hl build linked against openssl1.1. There's nothing wrong with linking openssl1.0 or anything else statically if it's not part of the OS anymore.
lpr
Sun, 2021/11/07 - 22:16
Permalink
to all SFOS users: please update your openssl.
Then a version linked against 1.1.1 is backward compatible
slava
Sun, 2021/11/07 - 22:31
Permalink
Oh come on. A version dynamically linked with openssl1.1 can't be backward compatible with the systems which don't have openssl1.1.
lpr
Mon, 2021/11/08 - 02:26
Permalink
just install 1.1 then it is
slava
Mon, 2021/11/08 - 04:26
Permalink
I can't do it for the user. And if the user is skilled enough to do it, then he/she must be skilled enough to install a variant of my app linked against openssl1.1 from already mentioned Chum. Right?
I did consider statically linking openssl1.1, but it didn't compile out of the box against sufficiently old SDK. So it's not as trivial as you're trying to make it sound.
3vixan
Thu, 2021/11/04 - 18:59
Permalink
Can I copy the last key file in another SFOS phone and reload the OTPs?
slava
Thu, 2021/11/04 - 19:27
Permalink
If you copy the key
~/.local/share/foil/foil.keyand encrypted files from~/Documents/FoilAuthto another phone, the secrets should get loaded. Note, however, that if you overwrite~/.local/share/foil/foil.keywith a different one, you lose access to the secrets encrypted with the old key. Be careful.Another (and safer) way to transfer OTP secrets between devices is a QR code - show it on one device and then read from the other, that works between devices with different keys. There is even a bulk sharing function on the Select page. No bulk import though (yet).
cquence
Sat, 2021/06/05 - 02:48
Permalink
I had to download the aarch64 rpm from the github page, somehow it was not available through Openrepos. Thanks for this great app. Migration from XA2 was easy using the QR code
slava
Sat, 2021/06/05 - 04:10
Permalink
Strange, aarch64 rpm is available from this page too. Anyway, I'm glad that you've got it installed one way or the other. Cheers!
MacGyver
Fri, 2020/10/23 - 02:33
Permalink
Just wondering, if you ever thought of having a way to backup things to SD card from app itself?
Now I have a script, that creates a backup of the files on my SD card, but its a bit of a hassle.
slava
Fri, 2020/10/30 - 06:05
Permalink
Yes, I did think about it (and even drafted a prototype) but decided to write a separate backup app instead, which would cover all my Foil apps at once and possibly any custom user-specified dconf/filesystem entries in addition to that. But that app isn't ready yet.
MacGyver
Fri, 2020/10/30 - 15:50
Permalink
Ok, cool, I will keep my eyes open for it then :)
MacGyver
Fri, 2019/11/29 - 03:49
Permalink
Are you adding HOTP support in near future? Id like to use this app instead of SailOTP, just cause it has the codes behind encrypted password and not open to everyone like SailOTP if they get access to phone.
I guess no need for import/export, cause you can just copy the
~/Documents/FoilAuthfile? Do I need to backup the~/.local/share/foil/foil.keyfile too? Just wanna know how correctly backup things, if anything bad happens to phone!I have multiple Jolla devices and would like to copy tokens to those too. How can I accomplish this?
Pages