iodine
iodine lets you tunnel IPv4 data through a DNS server. This can be usable in different situations where internet access is firewalled, but DNS queries are allowed.
It runs on Linux, Mac OS X, FreeBSD, NetBSD, OpenBSD and Windows and needs a TUN/TAP device. The bandwidth is asymmetrical with limited upstream and up to 1 Mbit/s downstream.
Compared to other DNS tunnel implementations, iodine offers:
Higher performance
iodine uses the NULL type that allows the downstream data to be sent without encoding. Each DNS reply can contain over a kilobyte of compressed payload data.
Portability
iodine runs on many different UNIX-like systems as well as on Win32. Tunnels can be set up between two hosts no matter their endianness or operating system.
Security
iodine uses challenge-response login secured by MD5 hash. It also filters out any packets not coming from the IP used when logging in.
Less setup
iodine handles setting IP number on interfaces automatically, and up to 16 users can share one server at the same time. Packet size is automatically probed for maximum downstream throughput.
Category:
Keywords:
| Attachment | Size | Date |
|---|---|---|
| 44.31 KB | 04/05/2014 - 01:22 |
- This made for a friend rzronline



Comments
rzr
Mon, 2014/05/19 - 22:34
Permalink
does nt it miss client ... i can try to rebuild mine if time miss
NielDK
Mon, 2014/05/19 - 23:40
Permalink
new
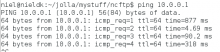
No, look at screenshots:
Server: (as root)
start iodine daemon: Since we cant use port 53, we will use port 5353
iodined -f 10.0.0.1 nieldk.com -p 5353
forward UDP port 53 to UDP port 5353, since we used port 5353 for iodined:
iptables -t nat -A PREROUTING -i wlan0 -p udp --dport 53 -j REDIRECT --to-port 5353
Client side:
iodine -f -r 192.168.0.91 nieldk.com
192.168.0.91 is your servers IP adress and nieldk.com a domainname that you can control, if you dont want to remember the server IP :) I had to use the IP, as I dont have a domainname ...
You will now get an IP of 10.0.0.2 on client and can ping server side with: ping 10.0.0.1 (we set that when we started iodined).